Security is an integral part of Selligent’s business and culture. From Product inception inside the development lifecycle all the way through the completion of each project, the security of our customers’ data is one of our top priorities.
This guide explains our security policies and procedures so that our customers can be confident that their data is secure.
Our office network and Software as a Service (SaaS) are physically separated: They are in different data centers and are using different routing to the internet. At the same time they are also managed by two different teams: The respective teams are the IT team and the SaaS operations team. These teams each report to different senior management.
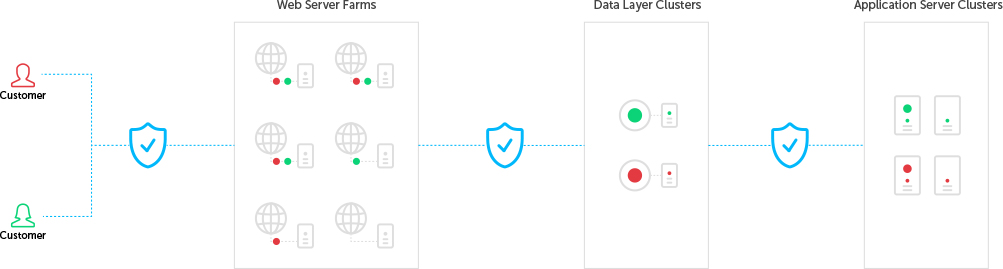
The following diagram shows the segregation in our SaaS architecture.
Selligent’s access control policy requires a unique username per environment and complex passwords.
The security team reviews the access control policy every year and user accounts are reviewed on a regular basis.
The Human Resources (HR) department is involved in the access control process for employees. HR can trigger events such as adding user accounts, moving user accounts, or deleting users.
The security and stability of our network is insured by a robust and redundant design including front-end, back-end and management firewalls.
Selligent manages every asset required to deliver our SaaS solutions. In addition, all operational activities on our infrastructure are carried out strictly under the control of Selligent employees.
Selligent’s operational controls address requirements for the execution of activities and the ability to review operational effectiveness. These controls also help maintain proper segregation of duties and access.
At Selligent, all employees are trained a minimum of once per year and attain a Selligent security certification as part of our security management system.
Selligent trains its developers and quality assurance personnel to check the quality and security of our application code. Training materials provided to these teams are aligned with the Open Web Application Security Project (OWASP) framework.
Our data centers provide state-of-the-art security and redundancy.
Our data centers are built with a multilayered physical security approach consistent with the requirements defined by Security Industry Standards. Access is controlled by photo badges, proximity access cards, biometric devices, CCTV/DVRs and alarms. Visitor access is strictly controlled.
Backup generators are equipped with enough fuel for several days and generators will activate approximately 1.5 minutes after a power failure. The UPS system manages the lag time between any power outage and the generator activation. All generators are redundant.
A highly sophisticated VESDA (Very Early Smoke Detection Apparatus) System provides very early warning of smoke or conditions leading to a fire by continuously sampling air in facilities for carbon products.
At Selligent, we have a security and privacy risk & incident handling process that addresses security risks or incidents.
The process defines the procedures to respond to potential incidents and includes a dedicated Security Team that is responsible for managing the response and fixing the security incident or privacy breach. This process includes incident investigations, prompt communication with customers, third parties and authorities, and impact assessments and improvements.
Selligent continuously monitors security alert sources for the latest information on new system vulnerabilities and proactively assess each of them against our environment. We also actively watch for updates from the providers of the technologies we use for security information.
Selligent’s solutions use industry standard cryptography for data in transit to and from our platform.
For SFTP/FTPS exchanges, the data files can be further protected by using PGP encryption software.
Selligent engages with a third-party web application vulnerability testing company to regularly assess each part of our application with a minimum of once a year as well as for any major release.
Selligent’s standard SaaS solution has backup media stored offsite inside a secondary data center.
The General Data Protection Regulation (GDPR) is adopted by the European parliament on 14 April 2016, and shall apply for 25 may 2018.
Selligent has appointed a Data Protection Officer.
Selligent is taking the necessary technical and organizational measures to comply with the requirements of the GDPR by its entry into force.
Visit Selligent’s GDPR Center for more details
Selligent invests on a permanent basis in information security and Privacy protection. Selligent efforts in these matters have been awarded by ISO certifications. The ISO certifications provide our customers with independent assessments and evaluations of Selligent’s security controls. These third-party evaluations are available upon request and include the following:






Selligent has attained compliance certification for ISO/IEC 27001:2013, the specification that defines the standard information security management system (ISMS). This security management standard specifies security management best practices and comprehensive security controls following the ISO 27002:2013 best practice guidance.
Organizations that meet the standard must be certified compliant by an independent and accredited certification body on successful completion of a formal compliance audit. The basis of this certification is the development and implementation of a clear security program.
Selligent has attained compliance certification for ISO 27701:2019, the first international standard for privacy information management. This universal framework allows organizations to efficiently operationalize compliance with new Privacy regulatory requirements.
ISO 27701:2019 defines a Privacy Information Management System (PIMS) as an extension of ISO 27001:2013 Information Security Management System (ISMS) creating a strong integration point for aligning security and privacy controls. The ISO 27701:2019 standard can be mapped to many of the requirements under GDPR, CCPA (California Consumer Privacy Act), or other law.
Selligent has attained compliance certification for ISO 27018:2019, the first international code of practice for cloud privacy. Based on EU data-protection laws, it gives specific guidance to cloud service providers (CSPs) acting as processors of personally identifiable information (PII) on assessing risks and implementing state-of-the-art controls for protecting PII.
An SOC 2 Type 2 report is an independent service auditor’s report that describes a service organization’s system and the suitability of the design and operating effectiveness of controls relevant to security, availability, confidentiality, and privacy.
“Hébergement de Données de Santé” (Health Data Hosting)
Selligent has attained HDS certification provided by the French government and health ministry of France, which sets the standard for sensitive health data protection. HDS certification signifies compliance for the secure and safe processing and storage of health data of French nationals.
Marigold: where relationships take root.